7 Fault Lines Shaping Enterprise Technology in 2026
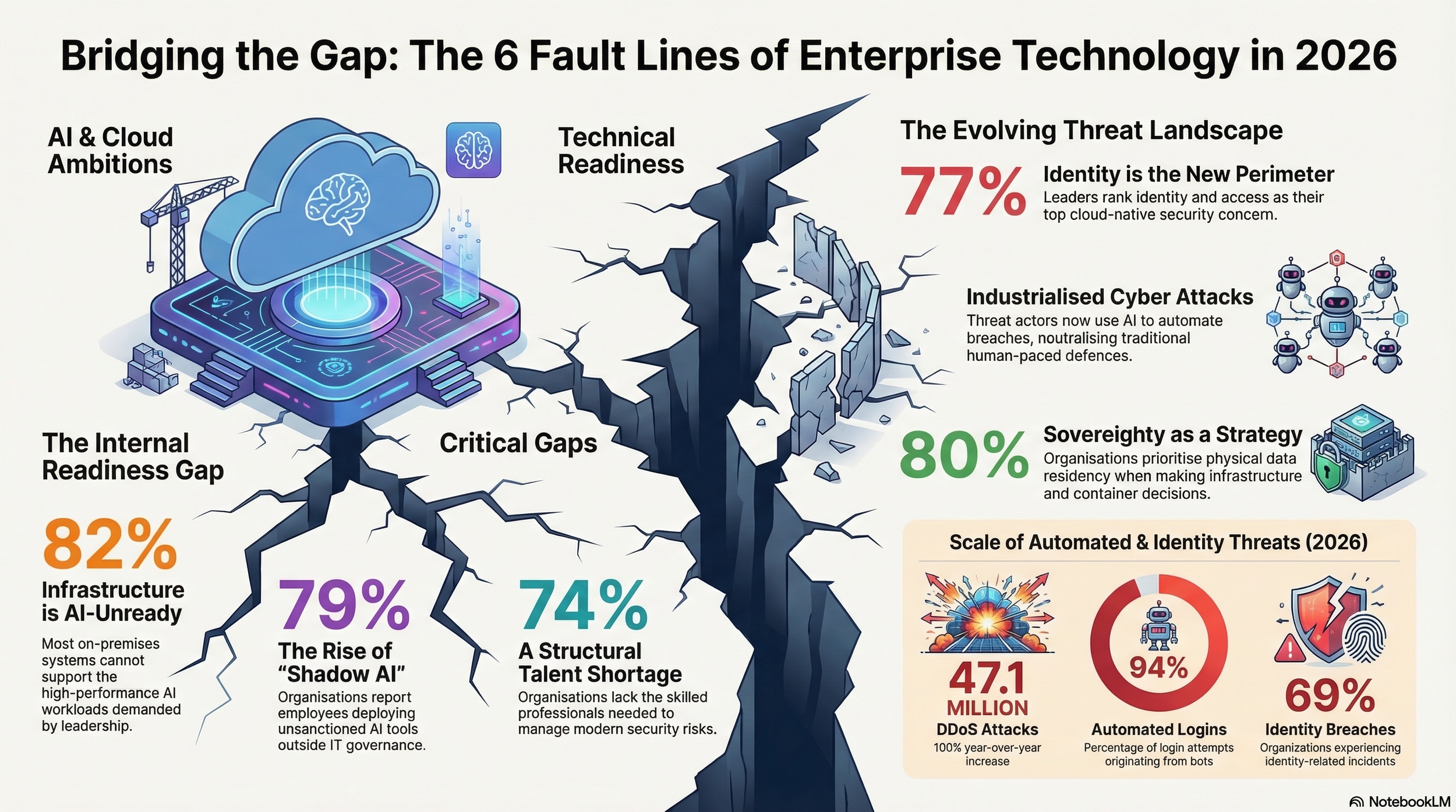
Enterprise technology in 2026 is defined by a paradox. Organisations are investing more than ever in artificial intelligence, cloud infrastructure, and digital modernisation. Budgets are rising. Strategies are in place. Deployment is accelerating. Yet across three of the most comprehensive industry reports published this year, the same uncomfortable truth emerges: the foundations are not keeping pace with the ambitions built on top of them.
The 2026 Nutanix Enterprise Cloud Index surveyed 1,600 senior IT and cloud leaders across 14 countries. The 2026 Cloudflare Threat Report draws on telemetry from a network that processes over 20% of global internet traffic. The 2026 Fortinet Cloud Security Report, produced by Cybersecurity Insiders, gathered insights from 1,163 cybersecurity leaders worldwide. Together, they offer a 360-degree view of an industry at an inflection point.
What follows are the seven fault lines that cut across all three reports — the structural weaknesses that, if left unaddressed, will determine which organisations lead the next wave of enterprise technology and which are consumed by it.
1. The Infrastructure Readiness Crisis
82% of organisations say their on-premises infrastructure is not fully prepared for AI workloads
The most striking number in this year’s research comes from the Nutanix Enterprise Cloud Index: more than four in five organisations acknowledge that their current infrastructure cannot fully support the AI workloads their leadership is demanding. This is not a problem of awareness. It is a problem of execution.
The Nutanix survey reveals that while 59% of organisations expect to run more than five AI-enabled applications within three years, only 60% had a concrete plan for AI-specific hardware such as GPUs and TPUs as recently as 2025. The gap between strategic intent and physical capacity is widening, not narrowing.
“The findings indicate organisations need enterprise-grade security, resilience, and portability as AI workloads can run anywhere. Organisations would also benefit from a common operating environment for virtual machines and containers that enables their IT leaders to scale AI confidently across hybrid environments.”
— Lee Caswell, SVP of Product and Solutions Marketing, Nutanix
Fortinet’s data reinforces this from the security side. Despite 62% of organisations expecting their cloud security budgets to increase, 59% still rate their cloud security posture at initial or developing stages. As the Fortinet report observes, this reveals a structural mismatch: budgets are rising, but maturity lags. The problem is not a lack of investment. It is that funding alone cannot close the gap when visibility, coordination, and architectural integration remain constrained.
Cloudflare’s threat researchers frame the consequences bluntly. Their inaugural Threat Report describes 2026 as the year of the total industrialisation of cyber threats, where the barrier to entry for attackers has vanished and operations that were once manual are now automated and scalable. Infrastructure that is not ready is not merely underperforming — it is exposed.
2. Shadow AI: The Risk That Arrived Faster Than Governance
79% of organisations have encountered unsanctioned AI deployments by employees outside IT
The Nutanix Enterprise Cloud Index reveals what may be the defining governance challenge of 2026: nearly four in five organisations report that employees outside IT functions are deploying AI applications and agents without authorisation. And 87% believe this shadow AI activity introduces tangible risk, from data exposure and intellectual property leaks to regulatory violations.
This is shadow IT reimagined for the generative AI era. Where previous waves of unsanctioned technology involved employees adopting cloud storage or messaging platforms, today’s shadow AI involves staff deploying intelligent agents and large language model-powered applications capable of ingesting, processing, and potentially leaking proprietary information at scale.
Cloudflare’s research validates this risk from the attacker’s perspective. Their report documents how AI LLMs have introduced what they describe as a dual-front risk. The unprecedented adoption rate means vast quantities of proprietary source code, financial details, and personally identifiable information are routinely funnelled into these systems — creating what Cloudflare calls a data gravity effect, in which the AI system itself becomes the most attractive target for exfiltration.
Fortinet’s survey confirms that AI and emerging technology security are now top-tier concerns, cited by 45% of respondents. Yet the challenge is not simply technical. The Nutanix data shows that the roots of shadow AI are organisational: 82% of respondents say silos between business units and IT make it difficult to execute technology initiatives effectively. When business teams cannot get the speed they need from centralised IT, they build or buy their own solutions — and governance falls through the cracks.
3. Identity Is the New Perimeter — And It Is Under Siege
77% of organisations rank identity and access security as their top cloud concern
If there is one theme that unites all three reports with unmistakable urgency, it is this: identity has replaced the network perimeter as the primary target for adversaries. Fortinet’s survey ranks identity and access security as the top cloud-native concern, ahead of misconfiguration and data exposure. And 69% of organisations experienced identity-related security incidents in the past twelve months.
Cloudflare’s threat intelligence provides the tactical detail behind this statistic. Their report documents a decisive shift among attackers from attacking the box to attacking the session. Using infostealers like LummaC2, adversaries now harvest live session tokens to capture already-authenticated states, effectively neutralising multi-factor authentication. Cloudflare’s analysis found that 94% of all login attempts originate from bots, and 63% of human logins involve credentials that have already been compromised elsewhere.
The threat extends beyond stolen credentials. Cloudflare documents the industrialisation of deepfake identities, with North Korean operatives using fabricated personas and AI-generated video to embed themselves in Western payrolls. These operatives maintain the illusion of domestic residency through laptop farms, creating what Cloudflare identifies as a new attack vector that places malicious insiders within an organisation’s most trusted systems.
Fortinet’s respondents echo the urgency. Their data shows that breaches rarely begin and end with a single vulnerability. Instead, attackers follow paths: a misconfiguration exposes a resource, a compromised or overprivileged identity enables access, and sensitive data becomes the target. These stages form what the Fortinet report calls an exposure chain — and most organisations manage each domain independently, only seeing how the segments combine in hindsight, after the damage.
4. The Containerisation Wave Is Transforming — But Not Simplifying — Enterprise IT
87% of organisations expect container use to increase over the next three years
Containerisation has moved beyond experimentation. The Nutanix Enterprise Cloud Index reports that 83% of organisations are already building new applications in containers, and 85% say AI is directly accelerating their adoption of containerised workloads. This is not a gradual shift. It is a structural transformation of how enterprise software is built, deployed, and managed.
Yet the Nutanix data also reveals that this transformation is layering new complexity onto infrastructure that was already struggling. In 2025, 81% of respondents said their IT infrastructure needed improvement to fully support cloud-native applications and containers. The 2026 findings suggest that while adoption has accelerated, the underlying challenges around infrastructure fitness, skills, and complexity remain very much alive.
Fortinet’s research provides the security dimension. Their survey shows 88% of organisations now operate across hybrid or multi-cloud environments, with 81% relying on two or more cloud providers. Every new provider, service, or identity adds configurations, permissions, and data paths. The attack surface does not just expand; it fragments. And Fortinet finds that 69% of organisations cite tool sprawl and visibility gaps as their top barrier to effective cloud security.
Cloudflare’s threat intelligence shows how adversaries are exploiting this fragmented landscape. Their report documents threat actors using a tactic they term Living off the XaaS — leveraging legitimate cloud services such as AWS, Google Cloud, and SaaS platforms to camouflage malicious operations within normal enterprise traffic. By exploiting tenant misconfigurations and overly permissive identity roles, attackers move laterally and operate undetected as what appear to be legitimate users.
“Across the Middle East and Africa, we’re seeing AI adoption move from experimentation to execution, but many organisations are trying to move faster than their infrastructure and operating models allow. To scale AI safely and confidently, organisations need a consistent, enterprise-grade foundation that brings IT and the business together across hybrid and multicloud environments.”- Mohammad Abulhouf, VP and GM for the Middle East and Africa, Nutanix
5. The Industrialisation of Cyber Threats Has Changed the Rules
47.1 million DDoS attacks observed by Cloudflare in 2025 — more than double the prior year
Cloudflare’s inaugural Threat Report delivers a stark message: 2026 marks the total industrialisation of cyber threats. The barrier to entry has vanished. What was once the province of sophisticated state-sponsored groups is now accessible to individual actors using low-cost AI subscriptions and commodity toolkits.
The numbers are staggering. Cloudflare’s network defends against more than 230 billion threats daily. DDoS attacks more than doubled in 2025, with network-layer attacks tripling year over year. The record-breaking attack peaked at 31.4 terabits per second — nearly six times the largest attack recorded in 2024. Most attacks lasted less than ten minutes, far too fast for any human-led mitigation.
But volumetric attacks are only part of the picture. Cloudflare documents how attackers are weaponising the SaaS supply chain. In one case, the threat actor GRUB1 compromised a single trusted integration between SaaS platforms and used generative AI in real time to navigate unfamiliar environments and locate high-value data — demonstrating that even unsophisticated actors can now execute high-impact breaches. Their analysts identified more than $123 million in explicit financial-theft attempts via email-based attacks in 2025.
Fortinet’s survey confirms that enterprises feel the pressure. Two-thirds of organisations lack strong confidence in their ability to detect and respond to cloud threats in real time — up from 64% the previous year. And only 11% report having autonomous remediation capabilities that can act without human intervention. Most automation remains alert-focused: identifying problems but leaving remediation to manual, human-paced processes. In an environment where attackers operate at machine speed, this gap is increasingly untenable.
6. Data Sovereignty Is No Longer a Compliance Checkbox — It Is a Strategic Imperative
80% of organisations say data sovereignty is a high priority in infrastructure decisions
The Nutanix Enterprise Cloud Index reveals that for the vast majority of organisations, where data physically resides has become as important as how it is protected. Eighty per cent of respondents say data sovereignty is a high priority when making infrastructure decisions, including where to deploy containers. More than half feel the need to run their infrastructure within a single country, driven primarily by security and data protection concerns.
This finding has particular resonance in the Middle East and Africa, where regulatory frameworks around data residency are evolving rapidly. But it is by no means a regional concern alone. Fortinet’s survey places data exposure and privacy at 66% of cloud security concerns, the third-highest category. And 54% of organisations experienced data exposure or privacy incidents in the past twelve months.
Cloudflare’s regional analysis adds a geopolitical dimension. Their report documents how nation-state actors are increasingly targeting telecommunications infrastructure — the very backbone through which data flows. Chinese actors have prioritised telecommunications providers for persistent pre-positioning, while Iranian groups have compromised government email accounts across the Middle East to send phishing campaigns to neighbouring state entities. In this environment, the question of data location is not merely regulatory. It is existential.
Nutanix’s 2025 ECI had already found that over 90% of respondents said data privacy was a priority when implementing GenAI solutions, yet 95% believed their organisation could be doing more to secure its models and applications. The 2026 data suggests that as AI workloads become more distributed and more targeted, sovereignty has moved from a compliance discussion to a boardroom-level strategic decision.
7. The Talent Gap Is Becoming a Structural Constraint
74% of organisations report an active shortage of cybersecurity professionals
Every fault line described in this article is amplified by a single underlying constraint: there are not enough skilled people to address them. Fortinet’s survey finds that nearly three-quarters of organisations face an active cybersecurity talent shortage, and 77% express high concern about the industry-wide skills gap. These shortages are especially acute in cloud-specific roles, where expertise must span infrastructure, identity, data, and application layers.
Nutanix’s research tells the same story from the infrastructure side. In 2025, skills shortages ranked as the second-greatest obstacle to scaling GenAI workloads from development into production, cited by 53% of respondents. IT training was the second-highest investment priority for organisations seeking to support generative AI. The 2026 data on organisational silos suggests the problem extends beyond headcount: even where talent exists, structural disconnects between business units and IT prevent effective collaboration.
Cloudflare’s threat intelligence underscores why this matters so urgently. Their research documents adversaries who do not face capacity constraints. Generative AI is enabling lone actors to execute operations that once required state-sponsored teams. Automated credential harvesting, AI-assisted exploitation of SaaS environments, and autonomous botnet attacks operate around the clock. Most DDoS attacks in 2025 concluded within ten minutes. The window for human intervention has effectively closed.
Fortinet’s report captures the resulting operational reality: overextended teams default to alert-driven workflows, triaging what they can and accepting that some signals will be missed. Proactive threat hunting, architecture improvement, and automation refinement are deprioritised due to lack of capacity. As the report observes, hiring alone cannot close this gap — even organisations that successfully recruit face lengthy onboarding cycles while cloud environments evolve daily.
The implication is clear across all three reports: organisations must invest not only in people but in platforms, automation, and architectures that reduce the burden on human operators. The alternative is a workforce perpetually running to stand still, while the threats and the technology estate continue to accelerate.
The Path Forward: Closing the Fault Lines
Read together, these three reports paint a picture of an industry at an inflection point. The building blocks of the AI-powered enterprise are being assembled: containers are becoming ubiquitous, AI agents are moving from concept to deployment, and organisations are investing heavily in modernisation. But the foundations are not yet solid.
Closing these fault lines will require more than incremental investment. It demands a fundamental rethinking of how infrastructure, security, governance, and talent come together. Organisations that treat infrastructure modernisation as a back-office concern will continue to fall behind. Those who recognise it as the strategic imperative it has become — inseparable from their AI ambitions, security posture, and competitive position — will be the ones who define the next era of enterprise technology.
As Fortinet’s respondents make clear, the shift is already underway. When asked how they would build their security strategy from scratch, 64% said they would choose a unified platform over a patchwork of point solutions. The preference is not for simplicity for its own sake. It is for architectures that can see across domains, act at machine speed, and scale with the environments they are meant to protect.
The fault lines are visible. The question is whether organisations will bridge them before they widen further.