Why Encryption Is Becoming National Infrastructure, and How SandboxAQ Is Productising It for the AI Era
By the end of 2025, something subtle but important had changed in how governments in the Middle East were talking about encryption. It was no longer framed as a technical safeguard to be checked off during audits or outsourced to security teams operating at the margins of decision-making. Instead, encryption was being pulled into the centre of national digital strategy, discussed alongside AI deployment, public-service digitisation, and economic competitiveness.
For SandboxAQ, this shift has shaped the way its cybersecurity products are being built, positioned, and deployed across the region. The company’s partnership with the Government of Bahrain, announced toward the end of the year, is less about a single implementation and more about a pattern SandboxAQ believes is emerging across the Gulf and parts of the wider Middle East.
“The government of Bahrain is really treating encryption as a national priority,” said Mohammed Aboul-Magd, Vice President of Product for Cybersecurity at SandboxAQ. “And it’s not happening in isolation. The UAE has rolled out a national encryption policy, Jordan has announced similar moves, and across the region there’s a recognition that encryption underpins everything governments are trying to do digitally.”
From a product perspective, that reframing matters. It changes encryption from a feature into a system-level requirement, and it changes the customer from an IT department into an entire government or enterprise operating at national scale.
The invisible dependency the product is built around
Encryption’s challenge as a product problem is that its value is largely invisible until it fails. It does not announce itself to users, and when it works properly, it disappears entirely into the background of everyday activity.
“Encryption isn’t something that’s top of mind for most people,” Aboul-Magd said. “But before you’ve had your first coffee in the morning, you’ve probably relied on it more than ten times — unlocking your phone, checking your bank account, making a purchase.”
SandboxAQ’s products are built around that contradiction. They assume encryption is already everywhere, embedded unevenly across networks, applications, endpoints, and legacy systems, often implemented years ago under assumptions about computing power that no longer hold. The task is not to introduce encryption where none exists, but to understand, modernise, and continuously adapt what is already there.
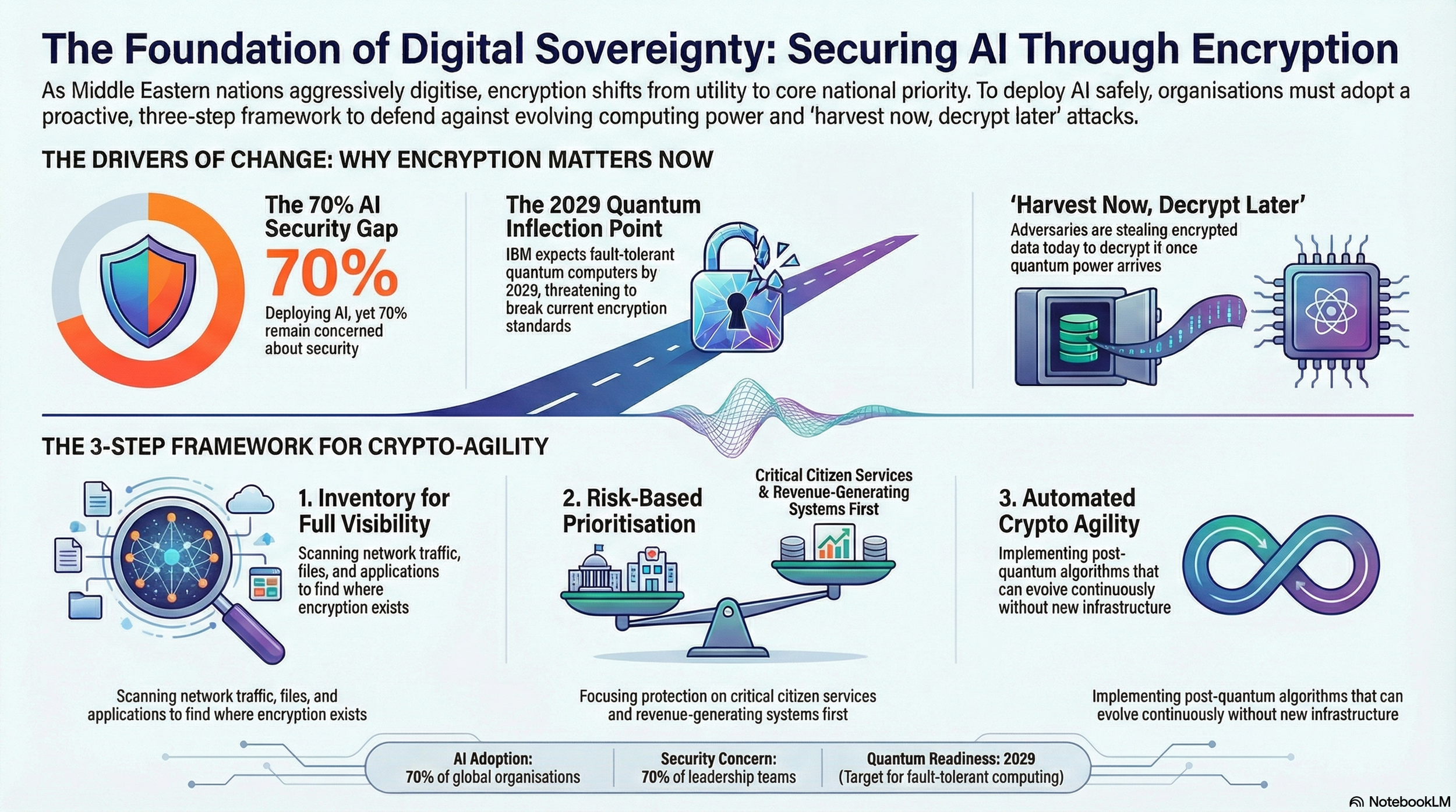
That need has become more urgent as computing power accelerates. AI has compressed attack timelines by automating discovery and exploitation, while quantum computing looms as a structural break rather than an incremental threat. IBM’s public expectation of a fault-tolerant quantum computer by 2029 has moved post-quantum security out of academic discussion and into product roadmaps.
“We’re already seeing ‘harvest now, decrypt later’ attacks,” Aboul-Magd said. “Adversaries are stealing encrypted data today and holding it until the computing power exists to decrypt it.”
Securing AI Through Encryption
Designing for AI-first governments
The regional context shapes the product requirements. Governments in the Middle East are deploying AI across citizen services, regulatory systems, and economic platforms at a speed that leaves little room for brittle foundations.
“Organisations in this region are at the forefront of deploying AI across their entire economy,” Aboul-Magd said. “To do that safely, you have to protect the AI itself, but you also have to secure the digital foundation it’s built on. That foundation is encryption.”
SandboxAQ’s core product response is ActiveGuard, a platform designed not as a point solution but as a continuous control layer for encryption risk. The product is structured around three operational steps that reflect how large organisations actually function, rather than how security frameworks often assume they do.
The first step is inventory. ActiveGuard scans network traffic, applications, endpoints, and file systems to identify where encryption exists, what kind it is, and how exposed it may be. This step alone, Aboul-Magd said, often surfaces gaps organisations were unaware of, particularly in environments shaped by decades of incremental technology decisions.
The second step is prioritisation. “Not all risk is created equal,” he said. A vulnerability in an internal test environment does not carry the same consequences as one in a citizen-facing service or a revenue-generating system. The product is designed to help organisations sequence remediation rather than attempt disruptive, all-at-once upgrades.
The third step is crypto agility, which is less about cryptography itself and more about institutional behaviour. ActiveGuard is built to integrate into development pipelines, procurement processes, and governance workflows so encryption standards evolve continuously as computing paradigms change, rather than being revisited every few years during major overhauls.
“This isn’t a one-time upgrade,” Aboul-Magd said. “Computing power will keep increasing, new encryption algorithms will emerge, and organisations have to be able to adopt them without breaking everything else.”
Building for legacy reality, not greenfield myths
One of the constraints shaping SandboxAQ’s product decisions is the persistence of legacy systems. Despite the rhetoric around AI-native governments and cloud-first strategies, much of the region’s critical infrastructure still runs on technology built decades ago.
Banks, defence organisations, and ministries operate hybrid environments where modern mobile applications sit alongside mainframes from the 1970s, 80s, and 90s. From a product standpoint, this eliminates any assumption that customers can “start fresh.”
“Starting from scratch is always easier,” Aboul-Magd said. “But that’s not reality.”
ActiveGuard is therefore designed to operate across heterogeneous environments, scanning everything from network traffic to compiled binaries, building what Aboul-Magd described as a full, end-to-end view of encryption risk. The product’s deployment model emphasises phased rollout and close collaboration, with prioritisation driven by operational impact rather than architectural purity.
“We prioritise together, we plan together,” he said. “That’s the only way complex environments actually get more secure.”
Extending the model to AI security
The same product logic now underpins SandboxAQ’s expansion into AI security, particularly around what the company calls “shadow AI.” As AI adoption has spread rapidly and informally, organisations are finding that models, agents, and tools are being used outside sanctioned workflows.
“Everyone is rolling out AI, and at the same time everyone is worried about the security implications,” Aboul-Magd said.
SandboxAQ’s internal survey found that more than 70% of organisations are deploying AI while expressing concern about the associated risks. Those concerns are grounded in real incidents, including sensitive data exposure through AI tools, employees unintentionally training external models on proprietary information, and reports of state actors using commercial AI systems to coordinate attacks.
From a product perspective, SandboxAQ treats shadow AI as a visibility and control problem rather than a moral one. Its AI Security Posture Management product applies the same principles as ActiveGuard: inventory what AI models, agents, and infrastructure are in use, assess their risk, and apply continuous controls to govern how they operate inside an organisation.
Shadow AI, Aboul-Magd noted, also includes supply-chain risk, where models downloaded from public repositories appear legitimate but contain hidden backdoors. The product is designed to surface those risks before they become incidents.
Notably, SandboxAQ has chosen not to position itself as an all-encompassing AI security vendor. When asked about deepfakes, Aboul-Magd acknowledged the concern but said it is not an area the company is focused on solving, a decision that reflects product focus rather than market hype.
Pricing the downside, not the feature set
As with any large-scale security product, cost is an unavoidable part of the conversation, particularly for governments and enterprises operating at national scale. Aboul-Magd said SandboxAQ deliberately reframes those discussions away from licensing and toward risk exposure.
“The conversations we have are less about cost and more about return on investment,” he said.
As economies become more digital and more AI-driven, the downside risk of insecure encryption and unmanaged AI grows disproportionately. From SandboxAQ’s perspective, its products are priced and positioned as protective infrastructure, designed to reduce systemic risk rather than optimise individual workflows.
What distinguishes the Middle East, Aboul-Magd argued, is not that it faces unique threats, but that it is acting earlier, embedding encryption and AI security into national digital ambitions rather than retrofitting them later.
“This isn’t something you finish and move on from,” he said. “New computing power will break existing encryption, new algorithms will replace them, and organisations that treat this as an ongoing discipline will be better positioned than those that treat it as a project.”
For SandboxAQ, the product bet is clear: in an AI-first world, encryption is no longer a background feature. It is the system everything else depends on.