The Year of the Evasive Adversary: How AI, Speed, and Trust Abuse Are Rewriting the Cybersecurity Playbook
The numbers are stark, and the message is clear: the adversaries are winning the speed race.
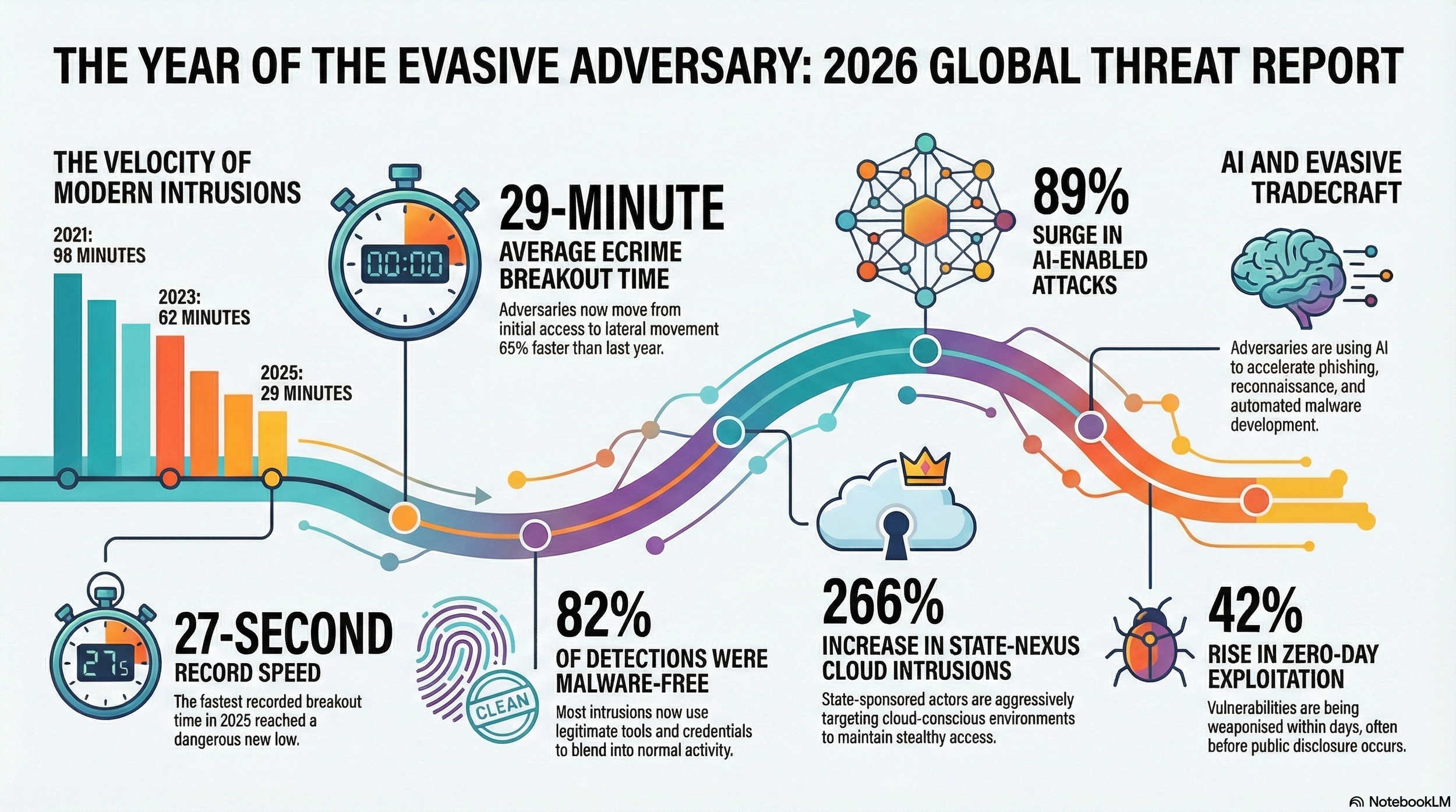
CrowdStrike’s 2026 Global Threat Report, released this week, paints a picture of a threat landscape that has fundamentally shifted. The average time it takes an eCrime actor to break out from an initial foothold and move laterally across a victim’s network has dropped to just 29 minutes—a 65% increase in speed compared to the prior year. The fastest recorded breakout took a mere 27 seconds. In one intrusion involving the threat group CHATTY SPIDER, data exfiltration began within four minutes of initial access.
These figures underscore the central argument of this year’s report: 2025 was the year that adversaries became truly evasive—not by hiding in the shadows, but by operating in plain sight, exploiting the very systems and relationships that organizations trust.
AI as Force Multiplier
Perhaps the most consequential trend documented in the report is the rapid adoption of artificial intelligence by threat actors across the sophistication spectrum. CrowdStrike observed an 89% year-over-year increase in attacks by AI-enabled adversaries, a surge that reflects both the democratization of AI tools and the speed with which criminal and state-sponsored groups have learned to exploit them.
The report details how adversaries are integrating commercially available AI models—including ChatGPT, Gemini, Claude, and DeepSeek—into multiple phases of their operations, from crafting convincing phishing lures to generating malicious code and automating post-exploitation activities. Forum discussions monitored by CrowdStrike Intelligence showed that ChatGPT was mentioned 550% more than any other AI model in underground communities throughout the year, reflecting its broad adoption even among criminal users.
One of the most striking examples came from Russia-nexus adversary FANCY BEAR, which deployed a novel Python-based malware called LAMEHUG. The malware used the Hugging Face API to interact with an open-source language model, generating system reconnaissance and document-collection commands through hardcoded prompts rather than traditional coded logic. While CrowdStrike assessed that LAMEHUG did not represent a meaningful leap in effectiveness over conventional malware, the case illustrates how state-sponsored actors are beginning to experiment with embedding AI directly into their offensive tooling.
Similarly, the DPRK-linked group FAMOUS CHOLLIMA incorporated multiple AI tools—including ChatGPT, Gemini, and GitHub Copilot—into its fraudulent employment schemes, using AI image-manipulation services to create fake personas and coding assistants to perform legitimate job functions while maintaining their cover.
The report cautions that while AI has so far primarily accelerated existing attack methods rather than creating entirely novel ones, the trajectory is concerning. More sophisticated actors are positioned to leverage agentic AI for operations requiring minimal human oversight, and some have already begun experimenting with autonomous frameworks. Evidence cited in the report indicates that certain threat actors have executed operations using agentic AI via tools such as Anthropic’s Claude Code and Model Context Protocol servers.
Malware-Free and Moving Through Trusted Pathways
The shift away from traditional malware-based attacks has reached a tipping point. According to the report, 82% of detections in 2025 were malware-free, up from just 51% in 2020. Instead of deploying executable payloads that trigger security alerts, adversaries are operating through valid credentials, trusted identity flows, approved SaaS integrations, and inherited software supply chains.
This approach, which CrowdStrike describes as exploiting trust at speed, makes detection extraordinarily difficult. When an attacker authenticates with legitimate credentials, navigates through an approved single sign-on flow, and accesses data via a standard SaaS application, the activity can be virtually indistinguishable from normal business operations.
The report highlights how ransomware groups in particular have refined this cross-domain tradecraft. Groups like SCATTERED SPIDER, BLOCKADE SPIDER, and PUNK SPIDER—the most active big game hunting adversary of 2025 with 198 observed intrusions, a 134% increase year-over-year—routinely moved across endpoints, cloud environments, hypervisors, and SaaS applications, deliberately avoiding heavily monitored systems.
In one notable incident, SCATTERED SPIDER gained initial access by social-engineering a help desk employee into performing a password reset, then dumped the Active Directory database from an unmanaged virtual machine within just three hours—interacting with only a single managed endpoint during the entire operation.
China’s Expanding Footprint
State-sponsored activity from China-nexus adversaries represented one of the most significant escalations documented in the report. CrowdStrike observed a 38% overall increase in China-nexus targeted intrusion activity, with attacks on logistics organizations surging 85%, telecommunications up 30%, and financial services up 20%.
These adversaries demonstrated a systematic preference for targeting network edge devices—VPN appliances, firewalls, gateways, and other internet-facing infrastructure—as their primary entry points. In 67% of the vulnerabilities China-nexus actors exploited, the flaw provided immediate system access, and 40% of those targeted internet-facing edge devices that often lack EDR coverage and consistent patching.
The speed of exploitation was particularly striking. Chinese state-sponsored groups consistently weaponized newly disclosed vulnerabilities within days of public release. VAULT PANDA and GENESIS PANDA both deployed exploits targeting a React Server Components deserialization vulnerability just two days after its public disclosure in December 2025. PHANTOM PANDA exploited a file upload vulnerability three days after vendor disclosure.
CrowdStrike assesses with high confidence that China-nexus adversaries maintain dedicated resources for monitoring vulnerability disclosures, enabling them to prioritize speed over operational security and exploit the narrow window between disclosure and patching. One long-running intrusion by WARP PANDA maintained persistent access for 22 months, from October 2023 through mid-2025, illustrating the long-term intelligence collection objectives behind these operations.
Supply Chain Under Siege
Supply chain attacks emerged as a defining tactic of 2025, enabling adversaries to bypass traditional security controls entirely by compromising the trusted software and services that organizations rely upon.
The most dramatic example was the PRESSURE CHOLLIMA attack on cryptocurrency exchange Bybit in February 2025, which CrowdStrike and the FBI described as the largest single financial theft ever reported. The DPRK-linked group compromised Safe{Wallet}, a digital asset management platform, by first targeting a software developer’s machine through a trojanized Python project. From that foothold, they pivoted to Safe{Wallet}’s cloud infrastructure, injecting malicious JavaScript that redirected a routine Bybit transaction worth $1.46 billion in cryptocurrency to an attacker-controlled wallet. Immediately after the theft, the adversary restored the malicious code to its original state to evade detection.
The npm ecosystem was also heavily targeted. In November 2025, attackers compromised 690 npm packages to distribute an updated version of the self-propagating information stealer ShaiHulud. In September, npm packages maintained by a single developer—accounting for more than 2 billion downloads per week—were compromised after threat actors phished administrative credentials, embedding code capable of monitoring network data and hijacking cryptocurrency transactions.
FAMOUS CHOLLIMA deployed more than 30 malicious npm packages between January and May 2025, combining them with social engineering to deliver malware to software developers under the guise of job recruitment assessments.
Cloud as the New Battleground
Cloud-conscious intrusions rose 37% in 2025, but the most alarming figure was the 266% increase in such intrusions by state-nexus threat actors. The report identifies a clear pattern: both criminal and state-sponsored adversaries are investing heavily in targeting cloud identity systems and SaaS platforms.
China-nexus adversary MURKY PANDA specialized in abusing trusted tenant-to-tenant relationships in Microsoft Entra ID, compromising upstream IT service providers to gain access to downstream victim organizations. Russia-nexus adversary COZY BEAR conducted sophisticated, multi-day social engineering campaigns that exploited interpersonal trust, organizational credibility, and Microsoft’s legitimate authentication infrastructure simultaneously. Victims were directed to enter credentials on genuine Microsoft login pages, eliminating the traditional phishing warning sign of suspicious domains.
Valid account abuse accounted for 35% of all cloud incidents, reinforcing the report’s thesis that identity has become central to modern intrusions.
Zero-Days: A 42% Surge
CrowdStrike documented a 42% year-over-year increase in zero-day vulnerabilities exploited prior to public disclosure, continuing a multi-year trend. The report notes that adversaries’ objectives shape their exploit selection: state-sponsored groups favor zero-days in edge devices for stealthy initial access, while eCrime groups like GRACEFUL SPIDER target internet-facing enterprise applications for maximum scale and speed.
GRACEFUL SPIDER, notable for its repeated use of zero-day exploits since late 2020, expanded its targeting in 2025 from file transfer applications to Oracle’s E-Business Suite, though the fundamental strategy remained consistent: exploiting internet-exposed enterprise web applications to achieve initial access and exfiltrate data. The report warns that this adversary’s sustained success will likely motivate other criminal groups to pursue similar capabilities in 2026.
Fake CAPTCHAs and Social Engineering at Scale
Beyond the sophisticated tradecraft of nation-state actors, the report documents a massive expansion in commodity social engineering techniques. CrowdStrike observed a 563% increase in incidents using fake CAPTCHA lures compared to 2024, as criminal actors shifted away from malicious browser update campaigns to this newer, more effective technique. Spam email volume rose 141% year-over-year, and rising cryptocurrency prices—Bitcoin up 55.1% and Monero up 88.5%—further incentivized extortion operations.
What Comes Next
The report’s recommendations reflect the severity of the findings. CrowdStrike urges organizations to treat AI security as a first-order priority, securing not just against AI-enabled threats but also protecting the AI systems now embedded in business operations. Identity and SaaS platforms should be treated as primary attack surfaces, and organizations must eliminate the cross-domain blind spots that adversaries are systematically exploiting.
Edge devices should be patched within 72 hours of critical vulnerability disclosure—a tight window, but one that reflects the reality of adversaries who can weaponize new exploits in as little as two days. Software supply chains require hardened developer environments, dependency validation, and continuous monitoring for anomalies.
CrowdStrike now tracks 281 adversaries, with 24 newly named in 2025 alone, including the first Belarus-nexus adversary, UMBRAL BISON. An additional 150 active malicious activity clusters and emerging threat groups are under observation. The scale is vast, and the sophistication is increasing.
As CrowdStrike CEO George Kurtz wrote in the report’s foreword, the world is now operating in an agentic era in which defending against AI-accelerated adversaries—and securing AI systems themselves—requires moving at machine speed. For security teams already stretched thin, the message from this year’s report is both sobering and urgent: the window to detect, decide, and respond has never been narrower, and the adversaries have never been more adept at making their activity look entirely normal.