Most Organisations Cannot Actually Recover Data from a Cyberattack. They Just Think They Can
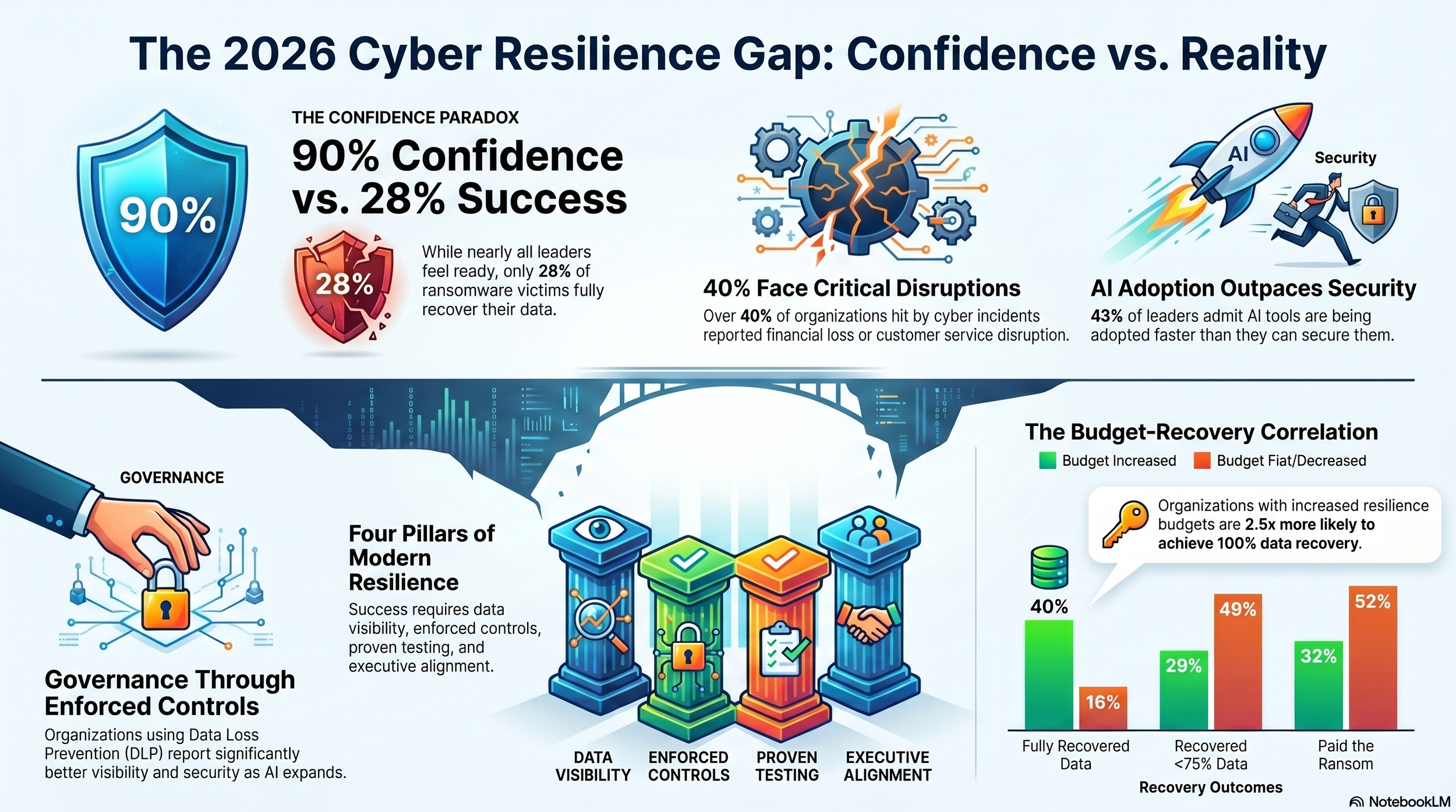
Fewer than one in three ransomware victims fully recover their data. Nine in ten security leaders believe they would. That is the most consequential finding in Veeam’s Data Trust and Resilience Report 2026, released today in Dubai and drawn from surveys and interviews with more than 900 senior IT, security, and risk leaders worldwide. The distance between those two numbers is not a rounding error. It is a market-wide failure to distinguish between believing in resilience and proving it.
The damage when that distinction becomes clear is significant. Among organisations hit by ransomware where operations or data were affected, only 28% fully recovered all affected data, and 44% recovered less than 75% of what was lost. When incidents occurred more broadly, 42% of affected organisations reported customer or constituent service disruption, 41% reported financial loss or revenue impact, and 38% experienced extended downtime of critical systems.
“Confidence in recovery from a ransomware attack is high, but the data tells a different story,” said Anand Eswaran, Chief Executive Officer at Veeam. “Even the most sophisticated organisations are discovering that confidence in recovery and proof of recovery are fundamentally different capabilities.”
The Illusion of Readiness
The report finds that most organisations conflate having a plan with having a proven capability. In interviews, security leaders frequently equated resilience with having backups, policies, or cyber insurance in place. But the survey data suggests those inputs do not reliably produce the outcomes organisations expect when a real incident strikes.
While 90% of respondents said they were confident in meeting their recovery time objectives, only 69% said those RTOs were fully aligned with business continuity goals. Many organisations are, in effect, measuring recovery readiness against targets that do not reflect what the business actually needs. The problem compounds when testing is infrequent: organisations that do not routinely test recovery under realistic conditions tend to overestimate readiness, discovering the shortfall only when an actual incident makes the gaps visible.
AI is widening that gap further. Security leaders describe it as having moved rapidly from experimentation to everyday execution, embedding itself in core business processes faster than policies and controls can follow. Forty-three per cent of respondents said AI tool adoption was outpacing their organisation’s ability to secure data and models. Forty-two per cent reported limited visibility into the AI tools in use across their organisation. Forty per cent said security policies had not yet been updated to address AI-specific risks, and 25% flagged shadow IT and unauthorised AI tool use as a primary concern.
“The infrastructure for deploying AI has rapidly outpaced the ability to secure it,” Eswaran said. “Organisations need end-to-end capabilities to understand, secure, protect, govern and ensure their data is resilient at machine speed.”
The governance challenge is also an ownership problem. AI and data risk governance most often rests with a single executive: 38% of respondents said the CISO owned it, 27% said the CIO, and only 17% reported a cross-functional governance structure. Given that AI risk spans cybersecurity, data governance, infrastructure, compliance, and business operations simultaneously, concentrating accountability in one role tends to create blind spots rather than resolve them.
What Separates Organisations That Recover
Despite variation across industries, sizes, and maturities, the survey identifies four practices consistently linked to stronger recovery outcomes. The first is expanded ownership: organisations that did not suffer an incident in the past year were more likely to use cross-functional policy approval committees, at 37% compared to 31% among those that did. The second is enforceable controls. Only 48% of respondents had data loss prevention in place, but those that did reported measurably better visibility as AI usage expanded, with AI outpacing security controls cited by 38% of DLP-equipped organisations versus 48% without.
The third is regular board-level communication. Organisations without an incident were more likely to report cyber risk to the board monthly or more frequently, at 56% versus 50% among those that experienced one. The fourth is meaningful metrics. The most commonly tracked KPIs included restore and recovery testing (57%), mean time to recover (56%), and time to isolate and contain (42%). Only 23% tracked fully automated recovery processes, illustrating how far most organisations remain from systematised resilience.
Budget tells a similar story. 49% of organisations increased cybersecurity spending year on year, while 51% stayed flat or decreased. Among those who invested more, 40% fully recovered their data after a ransomware attack, versus just 16% among those who did not. Budget-growth organisations were also far less likely to pay a ransom, with 32% doing so compared to 52% of those without increases. Regulatory pressure is adding further urgency: compliance mandates are now cited by 33% of respondents as a top emerging threat to data resilience, just behind cyberattacks at 36%.
“Veeam is redefining data resilience for the agentic era, where AI agents, apps, and data move faster than traditional controls,” Eswaran said. “The organisations that will lead tomorrow are those proving trust, not just believing in it.”
The report’s findings amount to a direct challenge to the security industry’s prevailing self-assessment. High confidence is not the same as demonstrated capability. Policies are not the same as enforced controls. Backups are not the same as a validated, tested, clean recovery. As agentic AI systems increasingly move data and trigger actions with less direct human oversight, the cost of confusing those things is rising.