Attackers Are No Longer Breaking In — They Are Logging In
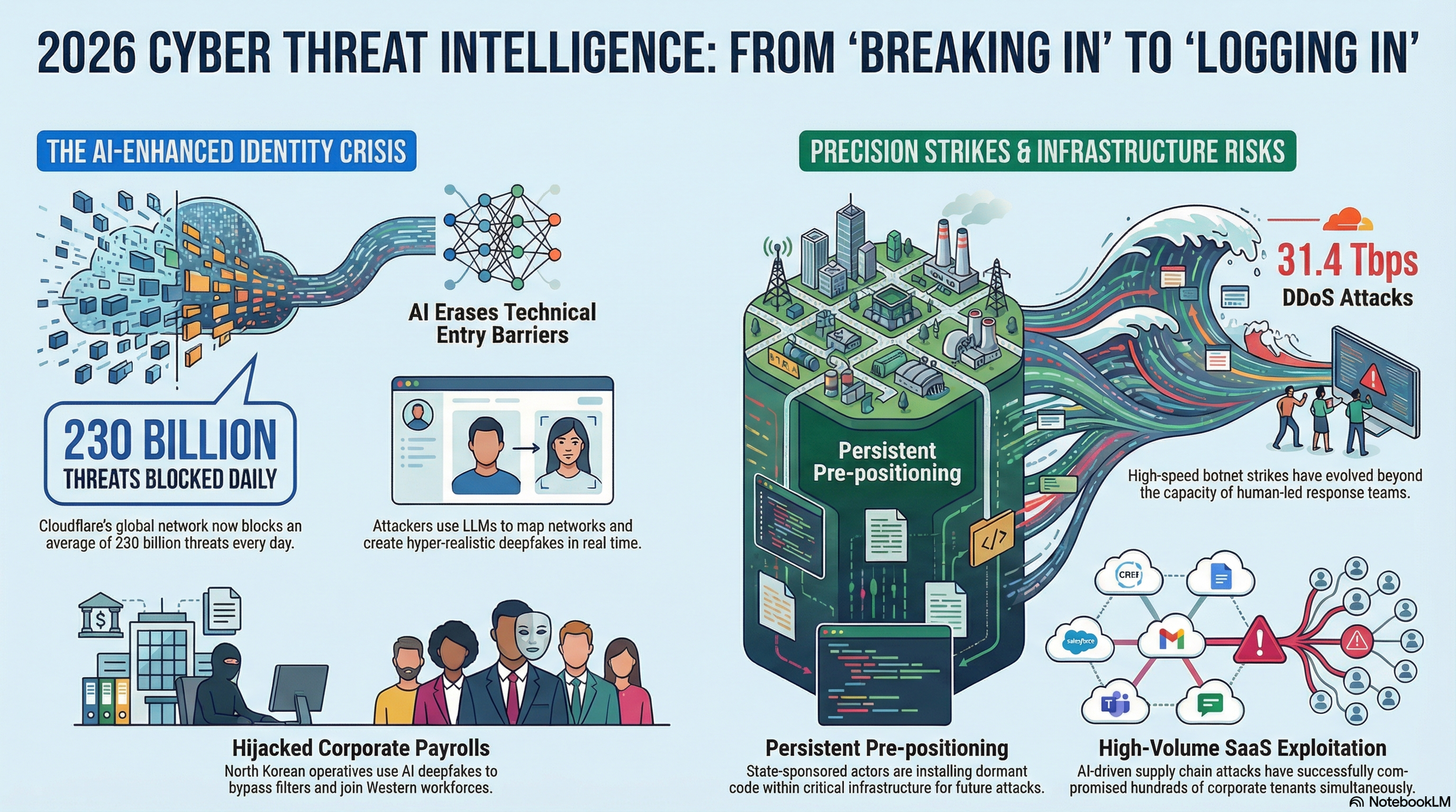
The internet was built on trust, its architects designed open protocols that assumed good faith between machines and the people who operated them. That assumption has now become the single greatest vulnerability in modern computing. Cloudflare’s inaugural 2026 Threat Report, drawn from the company’s vantage point protecting roughly a fifth of all global web traffic, makes the case with data that is difficult to dismiss: every day, the network intercepts more than 230 billion threats.
“Hackers thrive on the gaps left by fragmented, stale threat intelligence,” said Matthew Prince, co-founder and CEO of Cloudflare. “By sharing this intelligence with the world, we’re plugging the gaps and shifting the advantage back to the defenders. The result is a safer, more reliable Internet, where it is fundamentally more difficult and expensive for hackers to operate.”
The central finding is unambiguous: the traditional network perimeter is dead, and identity has become the primary battleground. In 2025, Cloudflare observed 47.1 million distributed denial-of-service (DDoS) attacks — more than double the previous year — yet the headline numbers mask a deeper transformation. Attackers are no longer trying to smash through the front door. They are logging in, armed with stolen credentials, hijacked session tokens, and AI-generated personas that pass for real employees.
“The message to defenders is simple: lead with intelligence or risk falling behind in a race where the stakes have never been higher,” said Blake Darché, head of threat intelligence at Cloudforce One.
The New Calculus of Risk
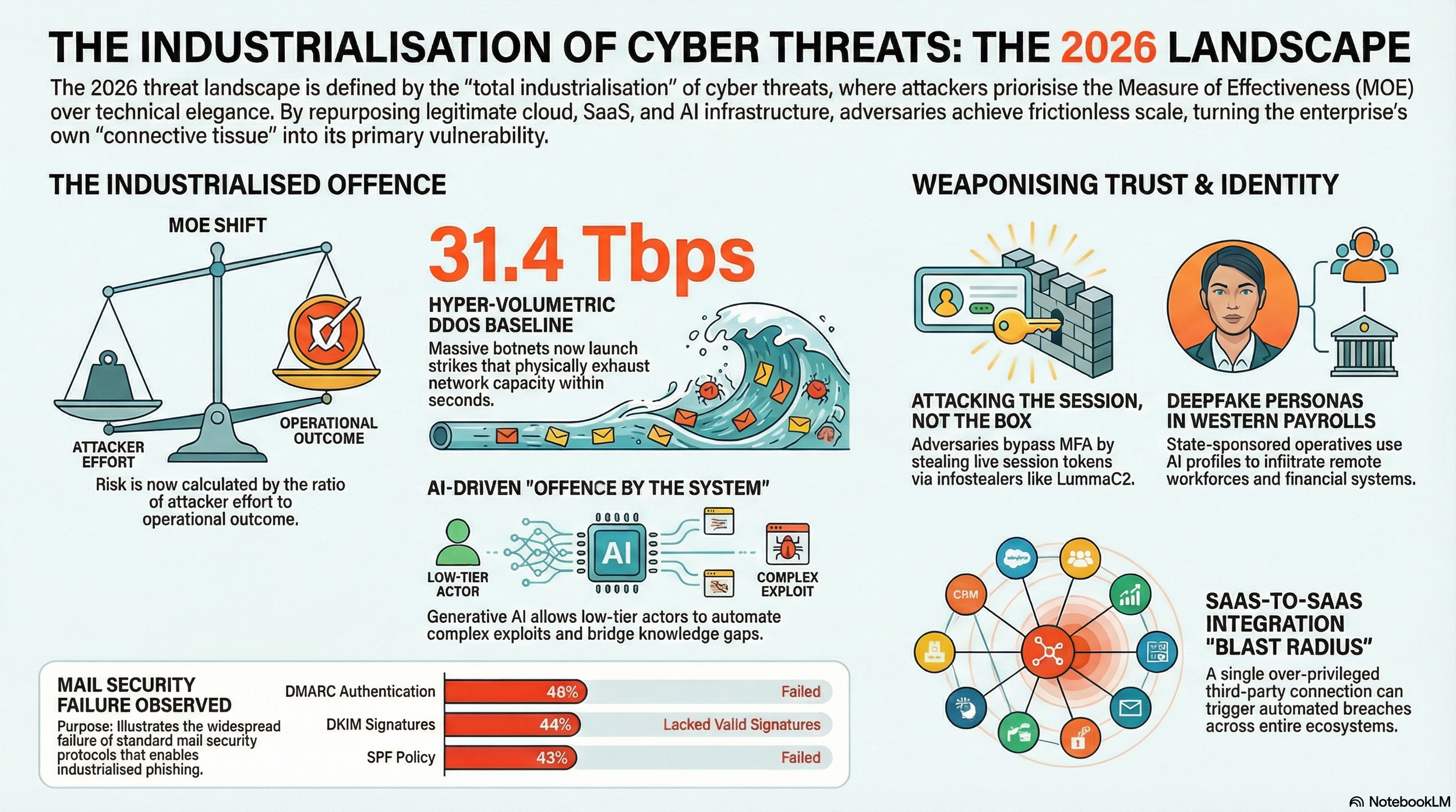
At the heart of the report is a concept Cloudflare calls the Measure of Effectiveness (MOE) — the ratio of attacker effort to operational outcome. For decades, sophistication was the yardstick by which security professionals gauged danger: the elegance of the code, the novelty of the zero-day exploit. Today, the metric that matters is efficiency. A high-MOE attack achieves maximum disruption at minimum cost.
Rather than spend millions developing bespoke exploits, a 2026 adversary might use a low-cost generative AI subscription to automate credential harvesting across thousands of targets simultaneously. The report documents how the threat actor known as GRUB1 compromised a single trusted integration between two SaaS platforms and, using AI to navigate unfamiliar database structures in real time, cascaded that breach across hundreds of corporate tenants. It is a model of ruthless economy.
AI: From Productivity Tool to Automated Exploit Vector
The report identifies a dual-front risk created by the explosion of large language models (LLMs). On one side, enterprises are unwittingly funnelling proprietary source code, financial details, and personally identifiable information into AI systems, creating what Cloudflare describes as a “data gravity effect” — where the AI system itself becomes the most lucrative target for future exfiltration.
On the other side, attackers are weaponising the same tools. An actor who previously lacked the skill to craft a convincing phishing email or write custom malware can now leverage an LLM to generate them at scale. Cloudflare’s product security team demonstrated this by using an AI coding tool called OpenCode to audit its own code, uncovering a critical exploit chain that allowed remote code execution through a combination of a simple URL override and an unsanitised markdown renderer. The exercise proved that AI dramatically lowers the cost of finding and weaponising vulnerabilities — a capability available to defenders and attackers alike.
The implication is clear: the historical emphasis on the inherent sophistication of a threat actor is becoming less relevant. What matters now is the velocity of the outcome and the sheer volume of automated, persistent campaigns.
Living off the Cloud
One of the report’s most striking findings is the extent to which threat actors have embedded themselves within legitimate cloud services that their targets already trust. Cloudflare tracks this pattern as Living off the XaaS (LotX) — a play on the established “living off the land” concept, extended to encompass the full spectrum of cloud platforms.
The Chinese state-linked group FrumpyToad, for instance, weaponised Google Calendar for command-and-control communications, reading and writing encrypted instructions directly into event descriptions. All traffic remained within Google’s encrypted ecosystem, never touching a malicious domain. The Russian group NastyShrew uses public paste sites as dead-drop resolvers, polling them to retrieve rotating command-and-control addresses. The Iranian-linked CrustyKrill hosts its operations on Azure Web Apps, blending seamlessly into reputable cloud traffic.
This tactic extends well beyond espionage groups. Legitimate bulk email services like Amazon SES and SendGrid are being exploited to launch phishing campaigns that bypass traditional spam filters. Cloud storage platforms such as Dropbox and Google Drive host malware payloads. GitHub is being abused for covert command-and-control channels. The network traffic resolves to reputable domains, making it extraordinarily difficult for security teams to distinguish between normal business operations and active threats.
The Four-Front Nation-State Threat
The report profiles operations from Russia, China, North Korea, and Iran — each pursuing distinct strategic objectives yet converging on a shared playbook of identity exploitation and cloud-native stealth.
Russian groups continue to blur the line between digital espionage and battlefield support. RottenShrew, a specialised reconnaissance unit, targeted Signal accounts used by Ukrainian military personnel, deploying a geolocation payload called PINPOINT to extract the precise coordinates of soldiers — intelligence with obvious kinetic applications. StainedShrew, publicly attributed to Russia by Dutch intelligence in May 2025, exhibited strategic opportunism by aligning its phishing campaigns with high-profile diplomatic events, from the NATO Summit in The Hague to the Brussels Indo-Pacific Forum.
Chinese actors, meanwhile, have moved beyond traditional bulk data theft towards what the report characterises as infrastructure pre-positioning. Salt Typhoon and Linen Typhoon have targeted North American telecommunications providers, government entities, and IT services — not for immediate espionage, but to embed footholds that could be activated during a future geopolitical crisis. PunyToad maintained persistent access to F5 BIG-IP systems for over a year, exfiltrating source code and documentation on undisclosed vulnerabilities.
North Korea’s contribution to the threat landscape is perhaps the most audacious. The report details an industrialised scheme in which operatives use AI-generated deepfakes and fraudulent identities to pass video interviews and embed themselves directly into Western corporate payrolls. These workers maintain the illusion of domestic residency using US-based “laptop farms” while accessing devices remotely from abroad, funnelling hundreds of millions of dollars in revenue back to the regime.
Iran, for its part, integrates digital espionage with kinetic military objectives. MuddyKrill accessed CCTV streams across Israel in June 2025 to provide real-time battle damage assessment during missile exchanges — a chilling demonstration of cyber-physical convergence.
The Industrialisation of Cybercrime
The nation-state threat is matched by a cybercriminal ecosystem that has achieved factory-level efficiency. Cloudforce One analysts identified over $123 million in explicit financial theft attempts through business email compromise (BEC) in 2025 alone. The average attempted theft sits at roughly $49,000 — a figure the report describes as calculated to be profitable yet small enough to bypass stringent executive approval thresholds.
Phishing has become a subscription service. Telegram-based phishing-as-a-service modules offer tiered pricing — $355 for 30 days — and guarantee 100 per cent inbox delivery by rotating clean residential proxies and warm IP addresses. These kits integrate adversary-in-the-middle technology that captures live session tokens, effectively neutralising standard multi-factor authentication. The attacker does not steal a password; they capture an already-authenticated session.
The infostealer-to-ransomware pipeline has become the primary engine of the criminal supply chain. According to Verizon’s 2025 Data Breach Investigations Report, 54 per cent of all ransomware attacks traced back to infostealer-enabled credential theft. Cloudflare participated in a global operation in May 2025 to disrupt Lumma Stealer, a malware-as-a-service platform that provided criminals with customised builds and professional dashboards for managing stolen data.
DDoS at Scale: When Human Intervention Is No Longer Fast Enough
The volumetric threat has escalated beyond what many organisations can absorb. In November 2025, the Aisuru botnet launched a UDP flood that peaked at 31.4 terabits per second — nearly six times the record set the previous year. Cloudflare recorded 19 new world-record DDoS attacks in 2025. Most lasted fewer than ten minutes, closing the window for any manual mitigation. On average, the company mitigated 5,376 DDoS attacks every hour.
The bot problem extends well beyond denial-of-service. Approximately 30 per cent of all HTTP traffic that Cloudflare observes originates from bots. A startling 94 per cent of all login attempts come from automated systems, and 63 per cent of human logins involve credentials that have already been compromised elsewhere. Attackers use tools like Selenium and Puppeteer to mimic human mouse movements and realistic scrolling, slipping past session-intelligence defences during credential-stuffing assaults.
The Email Authentication Gap
Underpinning much of this activity is a fundamental failure in email security infrastructure. The report reveals that nearly 43 per cent of emails failed Sender Policy Framework (SPF) checks, over 44 per cent lacked valid DKIM signatures, and 46 per cent failed DMARC. Link-based phishing remains the dominant threat vector, accounting for 25 per cent of all email detections, followed by identity deception at 19 per cent and brand impersonation at 16 per cent. The most impersonated brands include Windows, SANS, Microsoft, Stripe, and Facebook.
Attackers exploit a critical blind spot where mail servers fail to re-verify a sender’s identity after a message passes through a third-party gateway. Traffic arriving from a trusted relay causes the system to incorrectly treat spoofed external messages as internal or safe — a structural weakness that phishing-as-a-service operations systematically exploit.
What Defenders Must Do Now
Every major trend documented in this report — from AI-automated exploits to SaaS supply-chain pivoting, from deepfake job applicants to session-token theft — converges on the same point. Attackers are no longer trying to breach firewalls. They are impersonating trusted users, exploiting trusted integrations, and hiding within trusted cloud services.
For security leaders, this demands a fundamental shift in posture. The report recommends transitioning from standard multi-factor authentication to phishing-resistant alternatives such as FIDO2 and passkeys, with continuous session monitoring that can invalidate access the moment anomalous behaviour is detected. SaaS-to-SaaS integrations must be audited aggressively, with the principle of least privilege applied to every API token. Remote hiring processes need biometric verification and hardware-based geofencing. DDoS defences must be fully autonomous — the ten-minute attack window leaves no room for human decision-making.
The adversaries have industrialised. They operate at machine speed, across machine scale, using the very infrastructure their victims depend upon. The only viable response is defence that operates at the same speed and the same scale — built not around the walls of a network, but around the identity of every user, every device, and every integration that touches corporate data. Anything less, and you are simply leaving the front door unlocked.