The Crime Factory: How Cybercrime Stopped Being a Cottage Industry and Became a Corporation
The message arrived on a Tuesday morning, a wrong number, apparently, followed by an apology and then a brief, friendly exchange. The person on the other end seemed harmless, interesting even. They mentioned travel, asked thoughtful questions, and remembered details from one conversation to the next. Months passed, and a trust was built – this was of the kind that takes time. Then came the mention, almost as an afterthought, of a trading platform that had been performing quietly and reliably for years.
What the recipient of that first message could not have known was that the wrong number had not been wrong at all. That somewhere, someone had started their shift that morning by logging into a platform that looked, at first glance, like any other workplace dashboard. Open conversations to manage, colour-coded by priority. Scripts to follow. A summary of each contact — their profession, their savings, their family situation, and the last three things they had talked about.
An AI agent handling the routine messages, the good mornings, the check-ins, the small expressions of warmth that kept each relationship alive between sessions. All the operator had to do was step in at the right moments and move things forward.
The trading platform that the victim would eventually be shown existed only as a replica, indistinguishable from the real thing, built and maintained by a developer hired through a criminal marketplace for a flat fee. The people on the other side of those conversations believed they were building something real. They had no idea they were a line item in someone else's workflow.
This is not a story about one scam. It is a story about what happens when crime stops being a craft and becomes an industry. The lone hacker, hunched over a keyboard in a darkened room, belongs to a different era. What has replaced him is something far more unsettling: a fully operational service economy, with its own vendors, platforms, pricing tiers, and customer pipelines, in which almost anyone with an internet connection and a few hundred dollars can become a professional fraudster by the end of the afternoon.
A billion-dollar production line
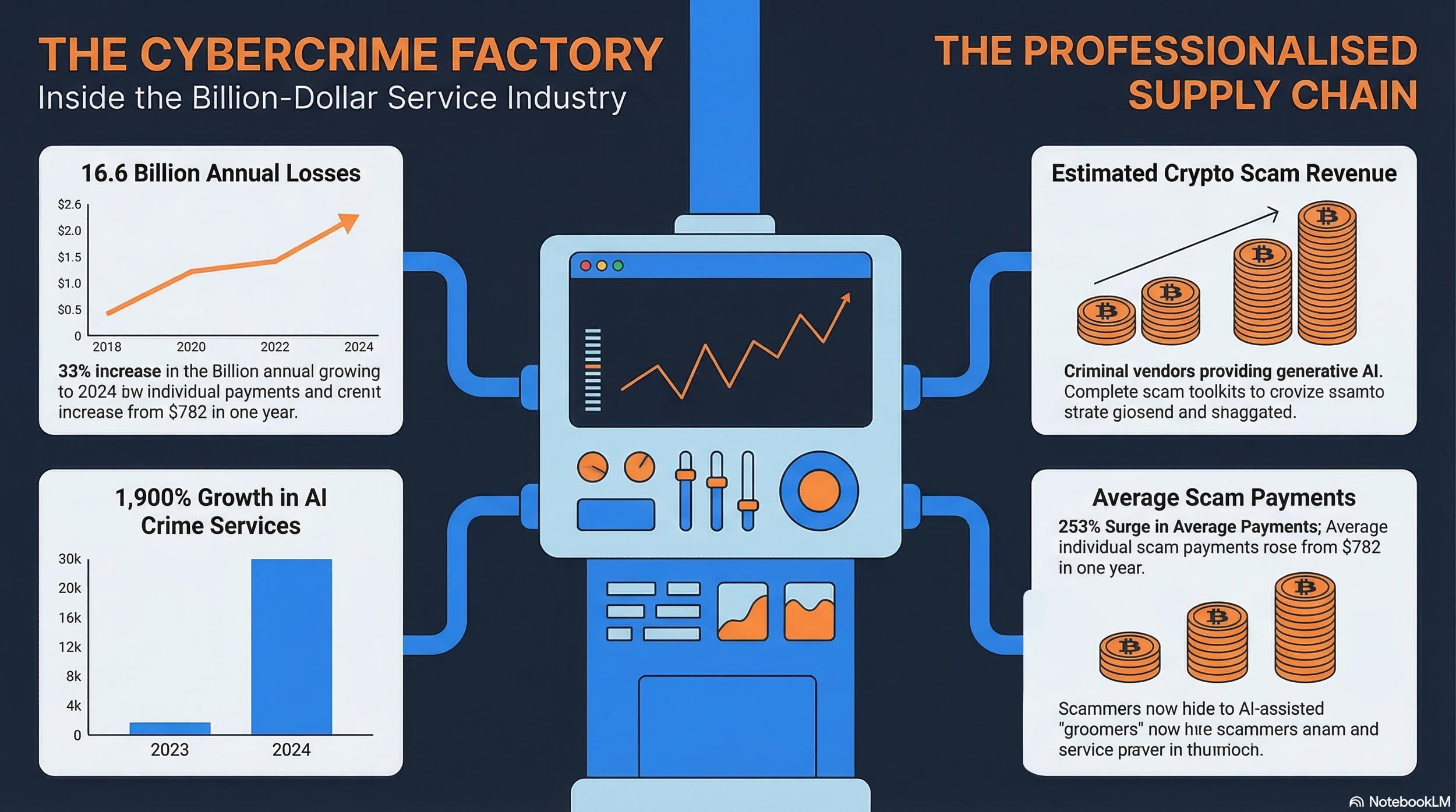
The numbers give the story its scale. The FBI's Internet Crime Complaint Centre's 2024 Annual Report, published in April 2025, recorded losses exceeding $16.6 billion across more than 859,000 complaints, a 33% increase on the prior year. Investment fraud, the category that encompasses pig butchering schemes, topped the list at $6.57 billion.
Separately, Chainalysis's 2026 Crypto Crime Report estimated that cryptocurrency scams received at least $14 billion on-chain in 2025, a significant jump from the $9.9 billion first reported for 2024, with projections suggesting the final 2025 figure could exceed $17 billion as further illicit wallet addresses are identified.
The average scam payment grew 253% year-on-year, from $782 in 2024 to $2,764 in 2025. Impersonation scams recorded a staggering 1,400% year-on-year growth rate. These are not the spoils of a few rogue hackers. This is industrial-scale crime.
Maël Le Touz, Threat Researcher at Infoblox, has spent years tracking the infrastructure that enables these operations. He explained that the professionalisation of cybercrime is not a sudden development. It follows a logic that legitimate industries would recognise.
"This is a very long trend, even outside of scams, where we see criminal groups getting more and more professionalised, and people suddenly realising that they can probably make as much money just selling the tools and not actually doing the slow part themselves," he said. The result is an ecosystem that functions less like a gang and more like a supply chain, with discrete actors each specialising in one link of the value chain: infrastructure, scripting, social engineering, and money movement.
Inside the platform
The mechanics of cybercrime-as-a-service are, in their way, impressive. Platforms, genuine software-as-a-service products built for criminals, offer everything a would-be scammer needs in a single interface: stolen social media accounts, AI-generated profile photographs, fake banking portals, and ready-to-use conversation scripts.
A stolen Instagram account might cost $5. A convincing bank account facade, $30. The scripts are granular, coaching operators on how to assess a target's wealth, family situation, and social isolation before proceeding. Chainalysis found that AI service vendors operating within criminal marketplaces recorded revenue growth of 1,900% in the years to 2024, as generative AI dramatically expanded the scale and convincingness of scam operations.
Le Touz described the experience of investigating one such platform. "They had an AI agent connected to WhatsApp. The AI would do the daily 'hi, how are you, I miss you, you're so beautiful,' and it would even translate the replies back so that the operator, without any knowledge of the victim's language, could just review and approve," he said. The AI also maintained a running summary of each victim's personal details, including family members, financial circumstances, and daily routines, so that operators could hand off conversations between shifts without losing continuity.
Inside these platforms, the labour is organised with uncomfortable rigour. Frontline operators handle the daily emotional grooming of victims, working through scripted exchanges that can span months. When a target is deemed ready, sufficiently trusting and sufficiently isolated, they are passed up the chain to a 'financial adviser' or 'bank manager' character who handles the actual investment fraud. The money, when it arrives, does not pass through the hands of the person who spent months building the relationship.
Le Touz explained how the platforms enforce this division of proceeds with technical controls built into the software itself. "The first-level scammer will have no access to the money. It will be wired automatically into the gang's accounts, where they can redistribute it. It's not democratic — it's very concentrated in a few hands," he said. Chainalysis estimated that enabling crime has become at least as profitable as committing it directly, with illicit-actor organisations accounting for $10.8 billion of the $40.9 billion received by illicit crypto addresses in 2024.
The arms race
Morey Haber, Chief Security Officer at BeyondTrust, has watched this evolution from the defensive side of the fence. He argued that what is unfolding is, at its core, a familiar dynamic in an unfamiliar new setting. "It becomes the typical arms race," he said.
"Many of the syndicates are using various attack paths that have no remediation, zero days, identity-based attacks that are non-defendable. The race becomes: can the good guys, the good companies and the governments, find them and patch them before someone else does?" The asymmetry is significant. Criminal syndicates operate without compliance requirements, ethical constraints, or the overhead of legitimate enterprise. They can adopt new attack surfaces within days, long before defenders have had time to assess the risk.
The infrastructure these operations exploit has itself become a weapon of concealment. Where criminal groups once relied on hosting providers in legally permissive jurisdictions, they have migrated to the world's largest cloud platforms, the same services used by billions of legitimate businesses every day. Le Touz described the challenge this creates for those trying to detect and block malicious activity. "The trend we're seeing is people using and abusing Cloudflare, Google, Amazon accounts, using cloud resources which makes it very hard for a business to detect, because you see connections going to the Cloudflare namespace, and everybody's using Cloudflare," he said. Domain lifespans have shrunk to days or even hours. Some fraudulent sites are accessible only via a unique password issued to each individual victim, meaning researchers cannot access them without actively engaging with a scammer.
This commoditisation of tooling has created a further problem: attribution has become nearly impossible. When every criminal group uses the same platform, the forensic fingerprints that once allowed researchers to identify specific actors disappear. Haber described how criminal syndicates scan the technology landscape with the same opportunistic attention that any venture capitalist might apply to a startup ecosystem. "They're looking at trends in the industry, just like businesses and consumers," he said. "And where they can introduce a component that can be weaponised and monetised, they are doing so." When a new AI coding tool drew hundreds of thousands of downloads in its first weeks on the market, syndicates had already planted a malicious connector in its open-source ecosystem, ransomware masquerading as a useful plugin.
Lowering the drawbridge
Perhaps the most unsettling dimension of this industrialisation is what it has done to the barriers to entry. Competition within the criminal marketplace is fierce and there are no intellectual property protections to keep rival groups from copying each other's tools. The effect is to push the cost of starting a scam operation towards zero. Interpol's Assistant Director of Financial Crime noted in 2025 that whereas criminal competence in the 1990s and early 2000s required reasonable technical skill, today's criminal marketplaces have removed that requirement entirely. According to Chainalysis, individuals can now access the tools and services needed to launch an operation for just a few hundred dollars.
Haber pointed to the speed at which criminals exploit the rush to adopt new technology as one of the defining features of the current threat landscape.
"History is literally repeating itself," he said. "We have to take the cybersecurity best practices that we've learned and apply them to the newer technology stack in order to defend." He was emphatic on the principle of secure by design: no technology, whether software, hardware, or consumer device, should reach the market without security built into the process from the start. The rush to ship fast and follow the latest trend has repeatedly proven to be an open door for criminal exploitation.
Building a defence
The World Economic Forum's Global Cybersecurity Outlook 2025 found that 72% of organisations reported a rise in cyber risks, while only 37% had processes in place to assess the security of AI tools before deployment. Haber argued that the cadence of security assessment must fundamentally change to match the speed of the threat.
"We need to move faster. Just because you ran a vulnerability scan last week doesn't mean you're still good. You have to be more continuous-minded, thinking: what is my state now, versus what it was even an hour ago," Haber said. Real-time continuous monitoring is now required. The FBI's 2024 Internet Crime Report shows that cyber-enabled fraud accounted for 83% of all financial losses reported to the IC3, highlighting how often organisations fail to see their exposure.
Le Touz is equally clear that no single actor, whether a cybersecurity company, a government, or a law enforcement agency, can address this alone. Criminal networks operate across multiple jurisdictions simultaneously, exploit gaps in international regulation, and are sophisticated enough to have a follow-up scam ready for victims who have already been defrauded, offering, for a fee, to recover their lost funds. "I really think collaboration is key," he said. "Those groups are tentacular — they have so many heads, and we see them in so many different places. There's no one-size-fits-all solution, no giant hammer to catch all of them." Infoblox works with cryptocurrency firms to follow the money on-chain, sharing DNS-level infrastructure data across the security community, a model that mirrors the interconnected nature of the criminal ecosystem it is trying to dismantle.
The trajectory is not difficult to read. Cybercrime-as-a-service is not a trend that is peaking. It is one that is maturing. Chainalysis's 2026 Crypto Crime Report documented the emergence of sophisticated money laundering networks offering full-service criminal infrastructure, supporting everything from fraud and scams to sanctions evasion. The tools are cheaper. The scripts are smarter. The AI does the emotional labour. And somewhere, on a messaging app or a platform that looks every bit as professional as a legitimate SaaS product, the next shift is already starting. The factory does not close.