The $60 Billion Problem: Why BeyondTrust Is Betting Everything on Identity
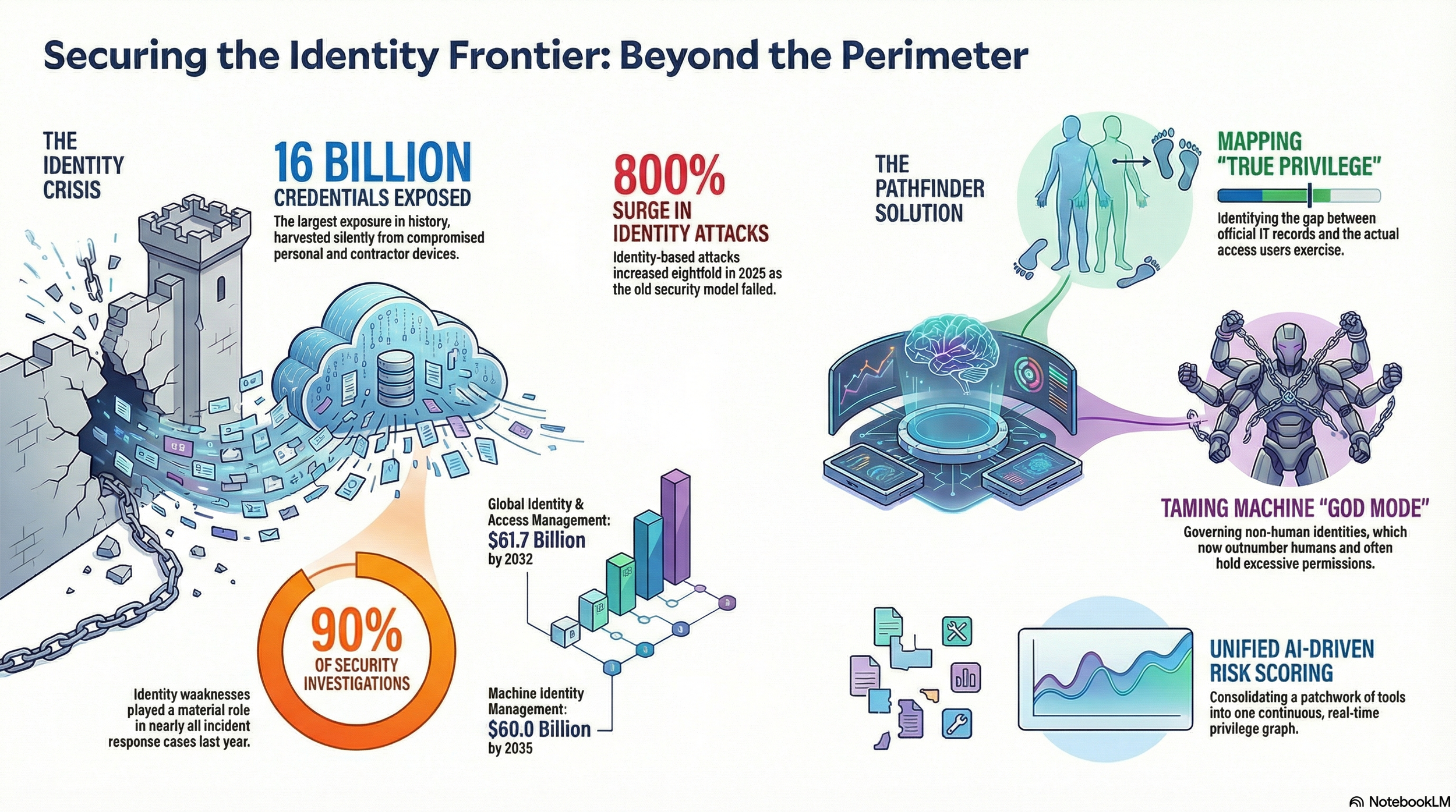
In June 2025, researchers uncovered what may be the largest credential exposure in history: 16 billion login credentials compiled from infostealer malware, phishing operations, and years of accumulated data breaches, surfacing in a single searchable database on the open web. No single company was hacked to produce it. The credentials had been harvested quietly over years from infected devices across the globe — employees' laptops, contractors' personal computers, systems that organisations didn't know were compromised. With one query, an attacker could pull valid usernames and passwords for virtually any major platform on earth.
It was, as security researchers noted at the time, not a technical event. It was an accounting of how comprehensively the old model of perimeter-based security had broken down. According to Flashpoint's Global Threat Intelligence Index, 1.8 billion credentials were stolen in the first half of 2025 alone — an 800% surge in identity-based attacks compared to prior periods. By year's end, the Identity Theft Resource Centre recorded the highest number of data breaches in history. And according to Unit 42's Global Incident Response Report 2026, identity weaknesses played a material role in almost 90% of all security investigations conducted last year, with identity-based techniques driving initial access in 65% of cases.
The attack surface has fundamentally changed. It is no longer primarily about protecting networks and devices. It is about controlling identities — and right now, most organisations are losing that battle.
The market has responded to all of this with urgency. According to Fortune Business Insights, the global identity and access management sector was valued at over $20 billion in 2024 and is projected to reach $61.7 billion by 2032. Meanwhile, according to Business Research Insights, the machine identity segment alone is expected to grow from $21.4 billion in 2026 to over $60 billion by 2035.
BeyondTrust, a global cybersecurity company, trusted by 20,000 customers, including 75 of the Fortune 100, has responded with Pathfinder: a unified, AI-driven platform that maps every identity in an environment, whether it belongs to a human employee, a software process, or an AI agent, alongside every privilege that identity holds and every pathway through which it could be exploited. Using AI, the platform continuously scores risk, surfaces the threats that matter most, and feeds remediation back to security teams without requiring a different tool for each step. Think of it less as a product and more as the connective tissue that most enterprise security stacks have been missing.
The Problem with The Patchwork
Every large organisation has, over years of growth and acquisitions and rushed technology decisions, ended up with a patchwork of security tools. There is usually something managing privileged access for IT admins, something else handling cloud access, another product for endpoints, and yet another for detecting threats. Each works reasonably well on its own. The problem is that they were never designed to talk to each other — and attackers have become very good at moving through the gaps between them.
Utsav Sanghavi, BeyondTrust's Director of Product Management for the Pathfinder platform, put it directly. "When security outcomes sit in separate products, customers bear the integration cost," he said. "They have to set up authentication in multiple places, authorisation in multiple places, and then try to stitch together visibility across systems. Even if each product is 'good,' the customer is forced into being the systems integrator. In today's environment, that's not realistic."
The result is what security professionals call uneven posture — different teams, different configurations, different blind spots. And as Sanghavi noted, uneven security is often worse than less security consistently applied. An attacker who understands where the joins are can slip through without triggering anything.
BeyondTrust built its reputation on privileged access management (PAM) — the practice of controlling and auditing access to critical systems by administrators and other senior users. It is foundational security work, and the company has done it long enough to know its limits. "Privilege doesn't stay inside the IT department anymore," Sanghavi said. "It spreads across the organisation, across cloud workloads, across SaaS, across endpoints, and increasingly across non-human and autonomous identities. PAM is very effective at what it does, but it doesn't automatically give you the full picture. And in security, not having the full picture is where risk hides."
The Access Nobody Logged
One of the more telling concepts in the Pathfinder platform is what BeyondTrust calls "True Privilege." It is the difference between the access a person is officially recorded as having and the access they can actually exercise across an organisation. That gap is wider than most security teams realise.
Here is how it typically happens. A company's IT department keeps careful records of who has administrator access to official systems. But business moves faster than governance. A sales leader signs up a new CRM tool and becomes its admin without IT ever knowing. An engineering team adopts a cloud development platform and sets their own permissions. A finance manager ends up with broad access to a workflow system because someone needed to solve a problem quickly and gave them the keys. None of this is logged anywhere central. None of it appears in the official directory.
Now, suppose one of those accounts is compromised. The attacker doesn't just get an email inbox. They inherit everything that account could reach — including admin-level access to systems nobody even knew were connected. The breach might look small on entry but devastating on impact.
"If you only assess direct privilege in the corporate IT layer, you could conclude: 'This person is fine,'" Sanghavi said. "But in reality, their indirect privileges may expose them and the organisation to threats. You can't get a meaningful risk rating if you ignore indirect paths."
Pathfinder addresses this through a component called Identity Security Insights, which maps accounts to identities, builds a picture of both official and unofficial access, and produces a combined risk score. That score is visualised as a live privilege graph — a dynamic map of every identity, access pathway, and potential escalation route across an organisation's cloud, on-premises, and hybrid environments, updated continuously rather than reviewed quarterly.
When Machines Took Over
The identity problem was already complex when it involved only humans. Then came the machines — and the calculus changed entirely.
A machine identity is not a person. It is any automated process, software agent, or system that has been granted credentials to access other systems. Service accounts, API tokens, cloud workload credentials, automated scripts — all of these qualify.
According to Business Research Insights, the machine identity management market is expected to grow from $21.4 billion in 2026 to over $60 billion by 2035, driven by the simple fact that in most large organisations today, non-human identities now outnumber human ones, and approximately 60% of cybersecurity professionals consider them a higher security risk. They are harder to track, rarely audited, and often granted far more access than they need.
The situation has been turbocharged by the rapid adoption of agentic AI — software systems that don't just follow instructions but reason, decide, and act on their own. Companies across every sector are deploying AI agents to automate workflows, process customer interactions, and manage internal operations. The rush to get these systems working has created a governance problem that most organisations haven't caught up with yet.
Sanghavi described a pattern he said he saw repeatedly with customers deploying AI. "Teams want outcomes fast," he said. "Organisations are focused on 'make the agent work.' To achieve that, they grant broad permissions so the agent doesn't fail. The unintended side effect is that the AI agent becomes overprivileged — it operates in 'god mode.'"
An AI agent with excessive privileges can traverse systems, pull sensitive records, execute transactions, and interact with external services without a human approving each step. When nobody has built a governance model around it — which is common in early AI deployments — the result is a new category of risk that most existing security tools were not built to detect or contain.
BeyondTrust CEO Janine Seebeck made the stakes plain when announcing Pathfinder's expansion into the UAE, India, Singapore, and South Africa. "The inability to see and control machine identities is no longer just a risk; it is a critical compliance failure," she said. "Pathfinder unites the visibility, intelligence, and control necessary to close these gaps."
A Market Worth Fighting Over – And Fiercely Contested
The space BeyondTrust is targeting with Pathfinder is one of cybersecurity's most commercially significant battlegrounds, and one of its most crowded.
PAM has historically been dominated by a trio — BeyondTrust, CyberArk, and Delinea — all of whom appear consistently in Gartner's Magic Quadrant for the category. But the broader identity security market has attracted a much larger field. Okta, Microsoft, SailPoint, and Ping Identity have all moved into adjacent territory, bundling PAM-adjacent capabilities into existing platforms as organisations look to consolidate vendors and reduce complexity.
CyberArk, widely regarded as BeyondTrust's most direct rival, has been particularly aggressive. Its $1.54 billion acquisition of Venafi in late 2024 was a clear move to deepen its machine identity credentials, and further acquisitions in 2025 expanded its identity governance coverage. SailPoint, which returned to public markets in early 2025 after a period of private ownership, has similarly been positioning itself across the identity governance space with ambitions that now overlap significantly with PAM territory.
Then there is Microsoft, which presents a different kind of competitive pressure altogether. Microsoft Entra ID is embedded in the workflows of hundreds of millions of organisations globally, and its PAM-adjacent capabilities have improved considerably. Competing against an installed base of that scale is not a product question — it is a positioning question. BeyondTrust's answer has been to argue that the breadth of the platform is not the same as the depth of specialisation, and that organisations facing sophisticated identity threats need the latter.
Where Pathfinder attempts to differentiate is in the argument that consolidation on a shared platform — one with a common intelligence fabric underneath it — delivers something that assembling capabilities from multiple vendors, however good those vendors are individually, cannot. Forrester's 2025 Wave for Privileged Identity Management noted BeyondTrust's "identity-first security strategy that helps organisations predict, discover, prevent, detect, and respond to identity risks in real time" as a distinguishing factor. That matters in a market where platform consolidation claims are everywhere and independent validation is scarce.
The Alert Fatigue Trap
There is a quiet crisis in security operations centres that rarely makes headlines but contributes meaningfully to breach statistics. Security teams are drowning in alerts — high volumes, poor context, limited time. The human response to sustained overload is to mute, to prioritise by gut feel, to eventually stop treating every alert as urgent. Attackers know this and factor it into their tactics.
"A lot of identity security approaches historically resemble noisy alert pipelines," Sanghavi said. "Someone has to manually weed through it and decide what matters. That model does not scale as environments get more complex, and it scales even worse in an AI-driven environment where identities and access paths multiply."
Pathfinder's architecture tries to tackle this at the source. Before a finding is surfaced as urgent, the system corroborates it — drawing on behavioural history, cross-signal verification, and threat intelligence from Phantom Labs, BeyondTrust's internal research team whose work involves actively simulating attacker behaviour to understand how identities and assets get abused in the real world.
On the question of automation, Sanghavi was measured rather than evangelical. He estimated that roughly 60 to 70% of deterministic remediation cases — where the right action is clear and the evidence threshold is met — can be automated effectively. Forcing a credential reset when a password appears compromised, for instance, is low-ambiguity and high-value. But for incidents that span multiple systems, involve unusual business context, or require human judgment about consequences, he said human oversight remains necessary.
"The platform's job is to reduce noise, corroborate, prioritise, and present actionable findings — not flood teams with raw alerts," he said. "Automation then becomes a response mechanism where appropriate, and human oversight becomes the escalation mechanism where necessary."
The Regional Push
Pathfinder's expansion into the UAE, India, Singapore, and South Africa is not simply about geographic coverage. Each market carries distinct regulatory obligations that are increasingly driving identity security investment.
In the UAE, the platform supports compliance with the National Electronic Security Authority's Information Assurance Standards, particularly relevant for critical infrastructure. In India, the Digital Personal Data Protection Act and CERT-In's incident reporting requirements are addressed through automated discovery and AI-driven risk prioritisation. Singapore's Critical Information Infrastructure operators can use Pathfinder to meet the Cybersecurity Code of Practice under the Cybersecurity Act. In South Africa, the platform helps organisations meet their obligations under the Protection of Personal Information Act, particularly as it applies to the machine identities that handle sensitive personal data.
The UAE holds specific importance for BeyondTrust, and Sanghavi was candid about what getting regional expansion right actually involves.
"If you expand recklessly, you create fragmentation and inconsistent trust," Sanghavi said. "If you expand deliberately, you can maintain uniformity at scale while still meeting local requirements."
For a platform whose entire value proposition is built on eliminating the inconsistency that comes from fragmented tools, that discipline applies as much to how it expands as to what it offers.
The Bigger Bet
In 2025, Marks & Spencer became one of the year's most-cited examples of what identity failure looks like at board level. A ransomware attack by the Scattered Spider group, executed through social engineering rather than any technical exploit, halted online orders, payments, and click-and-collect services for weeks and wiped hundreds of millions in market value. The breach exposed gaps in identity and access management and vendor risk oversight that many security leaders privately acknowledged were not unique to M&S.
According to Unit 42's Global Incident Response Report 2026, in 87% of all incident response cases last year, attacker activity crossed multiple attack surfaces simultaneously — meaning investigators had to trace behaviour across endpoints, identity systems, networks, and cloud services within the same intrusion. That is not a problem that any single-silo security tool is built to address.
BeyondTrust's argument with Pathfinder is that incidents like these are not anomalies. They are the predictable outcome of environments where privilege accumulates faster than it is audited, where machine identities proliferate without governance, and where the tools meant to provide oversight are too fragmented to deliver it.
Marc Maiffret, BeyondTrust's CTO, summarised the platform's ambition at launch. "Our AI-powered platform provides an integrated set of powerful tools for holistic identity visibility, just-in-time access, threat prevention, and detection," he said, "so customers can neutralise identity threats before they escalate."
Whether Pathfinder can deliver that at enterprise scale, against a competitive field that includes some of the world's largest technology companies, is the question the market will answer. What the breach record of the past two years has already answered is whether the problem the platform exists to solve is real. It is — and it is not getting simpler.